Identity document forgery is older than the documents themselves. A counterfeit Roman tessera turns up at almost every dig of a major imperial trading post. What changed in the last decade is not that fake IDs got better — they did, but slowly — but that the attackers got dramatically more efficient at producing them. A passable fake driver’s licence used to take a moderately skilled craftsperson hours to make. It now takes an unskilled person minutes with a laptop and a stable diffusion model.
That shift is the actual story. Most of the “how to spot a fake ID” guides you’ll read describe what fakes looked like in 2018: glued-on holograms, plain backgrounds, misaligned MRZ zones. Those signs still exist. They’re just no longer the primary signal in 2026.
This is a practical guide to what to actually look for, why the old advice is incomplete, and what businesses serious about preventing identity fraud should do instead.
What people actually fake, and why
Fake IDs come from three different worlds, and the people in each world want very different things.
Minors. A teenager who wants to get into a bar buys a $30 novelty ID, or — more often — borrows a real one from an older sibling or friend. Hospitality data is consistent on this: most fake IDs caught at the door are real documents in the wrong hands, not counterfeits. The economics are tiny. The fraud doesn’t compound. The bar that lets one through doesn’t lose the building. The risk is regulatory — a licence suspension if someone underage was served — not commercial.
Petty criminals. Mid-range fakes used for individual transactions: opening a bank account in someone else’s name, taking a loan on stolen credentials, buying controlled goods. These have to pass automated checks, not just visual inspection.
Organised crime and state actors. This is where the money is, and it’s also where most of the recent technical sophistication has gone. Europol regularly cites document forgery as a cornerstone of migrant smuggling, money laundering, and human trafficking operations. The fakes here are good — better than what most identity verification vendors will admit publicly.
The same vendor’s verification flow is asked to catch all three. Almost none of them are designed to.
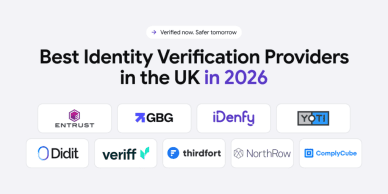
Automate your identity verification
See how iDenfy helps 1,000+ companies verify customers in seconds with AI-powered KYC.
Explore iDenfyWhat still works in visual checks
The classic checklist still holds, with caveats:
- A real hologram is embedded in the document substrate and shifts with viewing angle. A glued-on or printed hologram has a flat appearance and a faint outline where it was applied. This signal still works, but only in person — a remote photo capture can’t reliably reveal it.
- Tampering signs around the photo and edges. The single most common alteration is over-printing or pasting a new photo on a real document. Look for uneven lamination near the photo, discoloration where adhesive was applied, fonts that don’t match across fields, or ragged card edges where the laminate has been peeled and re-pressed. Cheap counterfeits also bubble or feel off when the card is gently flexed.
- The machine-readable zone. On passports, the two lines of monospaced characters at the bottom contain checksums. Calculate them — there are open-source Machine Readable Zone parsers that do this in three lines of code — and a forgery often fails the checksum even though the visible details look correct.
- The chip on e-passports. Modern passports carry a contactless chip with a digitally signed copy of the holder’s biometric data. A modern smartphone can read it via NFC using the BAC or PACE protocol with the MRZ as the access key. If a verification flow doesn’t read the chip on documents that have one, it’s leaving a high-confidence signal on the table.
- Document size and substrate weight. ISO/IEC 7810 ID-1 cards are 85.60 × 53.98 mm, the same as a credit card. Counterfeit cards often vary by a millimetre or feel either too light or too rigid. This is a fast in-person check that requires no equipment.
- The European Council’s Public Register of Authentic identity and travel Documents lists every officially issued document type, with photographs of security features. If the document doesn’t appear in PRADO, it isn’t a recognised format. The URL is prado.consilium.europa.eu — the single most useful free resource a small business has access to.
- Cross-checking the photo. The simplest check almost no one does: the person holding the document should look like the document’s photo. Forged documents are sometimes accompanied by a real-looking selfie of someone who isn’t the bearer.
What’s stopped working
The visual checklist was sufficient until about 2022. It isn’t anymore.
Generative AI has industrialised the production of fake document images. The cost of producing a passport photo that passes most automated checks has fallen by roughly two orders of magnitude in the last three years. The same tools produce realistic selfies of the person whose passport is being faked, which defeats simpler liveness checks.
The visible signs of fakery (misaligned holograms, off-colour tints) are exactly the signals an AI image model gets right. They’re trained on real documents. The remaining giveaways have shifted toward harder-to-detect technical signals: metadata stripped from a captured image, EXIF inconsistencies, screen reflections in an “in-person” capture, document substrate texture that doesn’t match real card stock.
In other words: the threat moved from the document to the capture process. The question isn’t “is this document real?” but “was this document, in this photo, actually held in front of this camera by this person?”
What businesses should actually do
The advice in older guides — “look closely, watch for spelling mistakes, check the holograms” — is still correct but no longer sufficient. Here is what’s worth doing in 2026, in rough order of cost:
- Use a verification provider that does passive liveness detection. The current state of the art analyses the capture for subtle 3D depth signals, screen reflections, and texture artefacts. Selfie-plus-blink (“active liveness”) was bypassed by deepfakes years ago.
- Cross-reference against authoritative registers, not just OCR. PRADO for European templates, the chip on e-passports, AAMVA for US driver licences (vendor-mediated), Interpol’s Stolen and Lost Travel Documents database for high-risk flows. None of these are perfect; a hit on any of them is close to dispositive.
- Capture the document in a controlled environment. Mobile capture in the vendor’s own SDK is meaningfully harder to spoof than allowing users to upload pre-existing photos. If a vendor accepts both, default to forcing in-app capture.
- For in-person verification, equip the floor with a UV light and a barcode scanner. UV light catches security features (laser-engraved imagery, fluorescent inks, security threads) a phone camera can’t see. A barcode scanner reads the data encoded on the back of most modern IDs — if the scanned fields don’t match what’s printed on the front, the document has been altered.
- Look at behavioural signals — automated and human. For automated flows: time-on-page during the capture, device telemetry, the IP geography of the capture vs. the document’s issuing country. For in-person checks: hesitation when asked to repeat the address or middle name on the card, eyes moving upward (a memory-recall pattern), or any reluctance to write a signature when asked. None of these prove anything alone; together they tilt risk scores meaningfully.
- For high-value transactions, require a separate factor. A document plus selfie with Proof of Address plus a phone number that can be checked against a carrier database is harder to fake at scale than any of the three alone.
- Train your manual review team on what fakes look like now, not what they looked like in 2018. Most internal training materials are years out of date. AI-generated fakes are the dominant category at the higher end of effort; the team should know how to spot the artefacts that betray them.
What none of this prevents
Even a well-implemented identity verification flow won’t catch every fraud. There are categories it structurally can’t:
- Genuine documents in the wrong hands. A real passport that someone other than the rightful holder is using. The only defences are biometric matching to the document chip (where present) and behavioural signals.
- First-party fraud. A real person using their real ID to commit fraud. Identity verification proves who someone is; it doesn’t prove what they intend to do next.
- A real person being forced to onboard while their attacker watches. Some flows now check for stress signals or duress patterns; most don’t.
These aren’t reasons to skip verification. They’re reasons to remember that verification is one layer of a defence, not the entire defence.
If you catch one
Most “how to spot a fake” guides stop at detection. What you do next matters at least as much.
For an in-person business: in most jurisdictions you have the legal right to refuse service, retain the document, and call the relevant authority. Use it. The standard workflow is to handle the document with gloves so latent prints aren’t lost, log the incident with date, time, and a photo of the document, and submit a report to the local police or licensing board within 24 hours. Most bars and retailers already have an internal compliance contact who knows the exact process — ask before you need it, not while it’s happening.
For a remote or online business: confiscation isn’t an option. The equivalent is to flag the account, freeze the in-flight transaction, escalate to your fraud team, and — for regulated industries — file a Suspicious Activity Report (SAR) with the relevant financial intelligence unit if the threshold is met. Don’t notify the user that you suspect fraud; that gives them time to move to a different platform with the same identity. Quietly review and then act.
Both processes have one thing in common: the value of catching a fake is largely lost if the data doesn’t propagate. The next vendor in the chain shouldn’t need to catch the same actor independently.
The honest conclusion
The “how to spot a fake ID” question used to have a checklist answer. It still does, but the checklist is less and less of the picture. The economics of forgery have shifted in the attacker’s favour, and the businesses that handle this best treat identity verification as a moving target rather than a one-time integration.
The classic advice — check the hologram, measure the card, validate the MRZ — is still correct. It is no longer enough. The next layer is process: who captured the document, in what environment, on which device, with what behavioural signals around the capture. The layer after that is institutional: how often the verification process is reviewed, how the manual queue is staffed, and how fast the flow updates when a new fake pattern surfaces in the wild.
Whichever vendor you use, ask them how they handle the AI-generated category specifically. The honest ones will tell you which attacks they catch, which they don’t, and what they’re doing about the gap. The dishonest ones will tell you they have it covered.